Data privacy laws in the US will change significantly in 2023. With five new state privacy laws taking effect, it can seem overwhelming to keep track of all the new requirements. Let’s break it all down so your business will be ready to comply with the new comprehensive privacy laws in California, Utah, Colorado, Virginia, and Connecticut.
There is no private right of action under any state privacy law. Each state has a specific regulator—such as the Attorney General or the California Privacy Protection Agency (CPPA)—that will enforce the law.
California Privacy
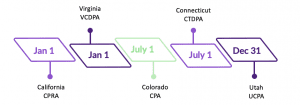
California (CPRA) | effective January 1, 2023
Companies are subject to the California privacy law if:
- They process the data of 100,000+ California residents OR
- 50% of their business revenue is derived from the sale/sharing of California residents’ personal data OR
- They have $25 million+ worldwide revenue
A crucial unique note about California: Employee and B2B data are exempted everywhere except California, so the CPRA will grant employees and business contacts the same rights as any other California resident.
Under California’s original privacy law, the CCPA, Californians have had the right to a privacy notice, to delete their data, and to opt out of selling their data. Under the new CPRA, which amends the CCPA, Californians will have additional rights, including the right to correct their data, port their data, opt out of sharing their data for targeted advertising, and limit the use and disclosure of sensitive personal information.
The CPRA expands the look-back period for businesses responding to data requests in California. When businesses receive a data request from a consumer, they will need to disclose information beyond the previous twelve months (which was the look-back period under the CCPA) for any personal information processed on or after January 1, 2022—unless doing so is impossible or would involve a disproportionate effort. As with many of the new issues under the CPRA, we are waiting for the CPPA to issue regulations clarifying what that exception means.
Also new under the CPRA is the consumer’s right to correct their data. Correction requests could be a little more complicated than they look in some situations. In order to prevent fraud, businesses may need to verify the corrected information. For instance, if an employee requests to change their social security number, the employer would need to be presented with supporting documentation like the new social security card.
California consumers can already opt out of the sale of their data. Starting in 2023, consumers will now be able to opt out of the sharing of their data as well. Sharing means cross context behavioral advertising where a business collects a consumer’s information across multiple platforms and collates that information in order to serve that consumer with a targeted ad. Businesses will need to post links on their website so consumers can opt out of both the selling and sharing of their data. There are some special rules around children’s data, and businesses will need to watch for more details from the CPPA about opting in for some data processing of consumers younger than 13 or between the ages of 13 and 16.
California has defined sensitive information as its own category of data. Sensitive personal information (PI) includes:
- Biometrics
- Contents of some communications
- Financial account information
- Genetic data
- Precise geolocation (within ⅓ of a mile)
- Government IDs
- Health data
- Race, religion, and union membership
- Sex life and sexual orientation
Companies doing business in California need to give consumers the right to limit the use of their sensitive data, including not keeping it any longer than is “reasonably necessary.” To implement this right, companies will need to provide notice and post a link on their website that says “limit the use of my sensitive personal information.”
The CPRA will require some changes in service provider and contractor obligations. Businesses need to have some control over their contractors and service providers. Service providers are required to bind subcontractors by written contracts to the same obligations that they’re working under, in addition to informing the business to the use of the subcontractor. Annual independent cybersecurity audits may be required of businesses if there’s significant risk involved in the processing of consumers’ data.
Data Protection Assessments, which the CPRA calls “risk assessments,” will need to be submitted to the CPPA on a regular basis. They will at least be triggered by processing sensitive personal information. Those assessments will need to weigh the benefits and risks to various audiences with the goal of restricting processing if the risks to the consumer outweigh the benefits to all stakeholders.
Data privacy triplets: CO, VA & CT
Colorado and Connecticut’s privacy laws are based largely on Virginia’s, which is a unique mix of California’s and Europe’s privacy concepts.
In these three states, a business must acquire affirmative consent from the consumer before processing any sensitive personal information.
Data Protection Assessments (DP Assessments) are required in Colorado, Virginia, and Connecticut for certain activities, such as processing sensitive data, selling personal data, processing personal data for targeted advertising, and profiling that has significant effects. Businesses can reuse DP Assessments that were done to comply with other jurisdictions. They don’t need to make them public, but state Attorneys General can access them upon request.
Consumers in these three states have the right to appeal. This means that businesses must have a process in place for consumers to appeal a denial of a consumer request within the business itself. If the business still believes the denial is accurate after this second look, it must provide instructions to consumers about how to contact the state Attorney General if they want to escalate the request.
Although these triplets share several qualities, they also differentiate themselves with a few unique regulations.
Colorado Privacy
Colorado Privacy Act (CPA) | effective July 1, 2023
Companies are subject to the Colorado privacy law if they:
- Control or process the personal data of 100,000 or more Colorado residents in a calendar year
- Sell any personal data and control or process the data of 25k+ Coloradans.
There are some unique exemptions under the Colorado privacy law. HIPAA covered entities are exempted in Colorado from coverage of the law entirely. Regarding FCRA & GLBA regulated entities, the data that is governed by those regulations is exempted, but the institutions are still covered by the law. De-identified data and publicly available information are exempt, but the data must be truly de-identified and meet a very specific definition of what’s publicly available.
Violation of the CPA is considered a Deceptive Trade Practice, which means that fines can range up to $2,000 per violation, not to exceed $500,000 total—or $10,000 per violation if the consumer is 60 years old or older with no cap on the total.
Virginia Privacy
Virginia Consumer Data Protection Act (VCDPA) | effective January 1, 2023
Compliance to Virginia’s privacy law is generally a bit simpler for businesses than the CCPA; however, it is stricter on a few key issues.
There are two thresholds for Virginia’s privacy law to apply to businesses:
- Control or process the personal data of 100,000 or more Virginia residents in a calendar year
- Control or process the personal data of 25,000 or more Virginians and derive over 50% of gross revenue from the sale of personal data
All organizations subject to HIPAA or Gramm–Leach–Bliley are exempt, as are non-profits and institutes of higher education. Although de-identified data and publicly available information are exempt from this law, there are strict requirements for categorizing data this way. Pseudonymous data is exempt from some things like rights requests.
Fines for violation can be up to $7,500 per violation (plus attorney fees). There is a 30-day cure period for businesses to fix any violations. Money collected goes into a Consumer Privacy Fund to support AG enforcement efforts.
Connecticut Privacy
Connecticut Data Privacy Act (CTDPA) | Effective July 1, 2023
There are two thresholds for Connecticut’s privacy law to apply to businesses:
- Control or process the personal data of 100,000 or more Connecticut residents in a calendar year
- Control or process the personal data of 25,000 or more Connecticut residents and derive over 25% of gross revenue from the sale of personal data
Consumers whose data was used only for payment processing are excluded from the total number of Connecticut residents’ data in the applicability threshold. Like California, there is an authorized agent process. Starting in 2025, there will be a global opt-out requirement, such as via a browser extension that can signal to websites visited by consumers to not track or sell their personal data. Interestingly, this is not allowed to be a default setting; consumers will be required to manually toggle the opt-out button.
At 60 days, Connecticut has the longest cure period of these five state laws, but it will become optional in 2025. After that, the Attorney General will be able to start an enforcement process immediately following an alleged violation.
Penalties for violating the law range from $2,000 to $10,000, with higher penalties for violating the rights of senior citizens.
Utah Privacy
Utah Consumer Privacy Act (UCPA) | effective December 31, 2023
Utah’s privacy law is broadly based on Virginia’s privacy law, with a few business-friendly tweaks. The Utah privacy law’s applicability is unique in that, in order to be subject to the law, companies conducting business in Utah need to both have an annual revenue of $25M and either process personal data of 100,000+ Utahns or derive 50%+ revenue from the sale of personal data and processing personal data of 25,000 Utahns. In other states with comprehensive consumer privacy laws, businesses need to meet only one of those requirements. So fewer businesses will be subject to the UCPA than other state privacy laws.
Unlike California’s privacy law, Utah’s privacy law does not have the option for consumers to limit the use or disclosure of sensitive personal information, but it does stipulate that before businesses process sensitive personal data, they have to present the consumer with clear notice about that, and then present them with the opportunity to opt out of the processing.
Consumer rights in Utah are similar to the other state privacy laws. But the right to deletion and the right to access a portable version of their data are limited to personal data that the consumer has provided to the business. So if a consumer asks a company to delete their information, the company only has to delete the information that the customer gave them. It’s unclear in practice how feasible that will be to distinguish, so companies might choose to have deletion and portability that is just as broad as in other states.
Some notable requirements are missing from Utah’s privacy law. There is no regulation of profiling or automated decision-making. There is no requirement for Data Protection Assessments. There is no appeals process for denied rights requests. There are no authorized agents, where a consumer can give someone else the authority to make these requests on their behalf. And there are no additional instructions for implementing regulations, so the text of the law is what we get.
In most states, there is one regulator that will enforce their privacy law—such as the Attorney General or California’s CPPA. Utah has a unique, two-tiered process for enforcement of the law. First, the Division of Consumer Protection inside the state’s Department of Commerce must receive complaints and do a brief investigation. If they find evidence of a violation, they may then refer it to the Attorney General to enforce. So the Attorney General on its own can not start enforcement actions.
At $7,500 per violation, the possible fines for violations are higher in Utah than other states, but there is a substantial cure provision. Businesses will generally have 30 days to fix the violation.
Check out our free webinars
SixFifty’s privacy experts presented this and much more information in four invaluable 30-minute webinars in September and October 2022. Visit our webinars page to watch the 4-part 2023 US Privacy Roadtrip, on demand:
- Privacy Overview
- Implementing a Privacy Program
- Operationalizing a Privacy Program
- Portals and Requests
SixFifty’s Privacy Docs
SixFifty’s US Privacy sets businesses up for compliance throughout the entire United States. This one-of-a-kind tool allows companies to generate a set of privacy compliance documents for the laws applicable to their business. Plus, we notify our subscribers when a law has changed and their documents need a refresh. As more states pass similar laws, we update our tools to make sure our customers’ documents are always in compliance.
Want to see how it works? Book a demo with us today.